511
How does the tapping of mobile phones and how to protect themselves
How to listen to conversations on cell phones, is it possible to defend against such attacks and as a subscriber to determine that his phone is tapped? In the light of recent espionage scandals these questions again are on the agenda. AIN.UA asked the Ukrainian mobile operators to tell you what to do in such cases.
Surprisingly, many market participants to respond to these questions was not a full answer we only got from "MTS Ukraine". Life :) has not responded to the request at all, and in Kyivstar, said that the operator is not an expert in such matters, therefore advised to address for comments to representatives of civil service. In addition to the responses of MTS, we used the information about surveillance from public sources.
As operators protect their networkTechnology GSM was originally developed and implemented taking into account the requirements of state authorities on the level of security. To maintain this security, most countries in the world prohibit the use and sell of powerful encoders, scramblers, cryptobranchoidea, as well as a very secure technology public relations. Themselves operators protect their radio channels by means of encryption, using quite complex algorithms. The choice of cryptoalgorithm is at the stage of establishing a connection between the subscriber and the base station. As for the probability of information leakage of user from equipment operators, MTS argued that it is reduced to zero because of the complexity and testability of object access and equipment.
How to "listen" phones
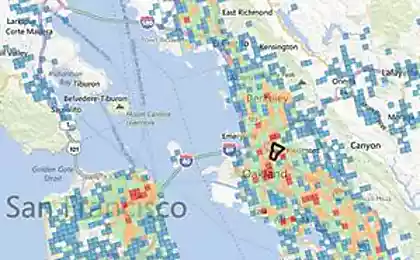
There are two methods of listening to customers — active and passive. For passive listening subscriber would require the use of expensive equipment and specially trained personnel. Now on the grey market you can buy complexes with the help of which you can listen to subscribers within a radius of 500 meters, the cost starts from several hundred thousand euros. They look like the picture on the right. The Internet easily can altipiani such systems and how they work.
Manufacturers of such equipment claim that the system allows you to monitor GSM calls in real time, based on access to the SIM card of the object or the database operator. If such access is not, the conversations you can listen to with a delay, depending on the level of encryption used by the operator.The system can also be part of the mobile complex to monitor and listen to the moving objects.
The second way of listening isactive essential intervention in the management protocols and authentication with the help of special mobile complexes. Such equipment, despite its apparent simplicity (in fact, this is a pair of modified phones and computer), can cost from a few tens to hundreds of thousands of dollars. Working with such systems requires highly skilled personnel in the field of communications.
The principle of this attack is the following: the mobile complex due to a closer location to the subscriber (up to 500 m) can "capture" signals for connection establishment and data transfer, replacing the nearest base station. In fact, the complex becomes a "mediator" between the subscriber and the base station with all its attendant security problems.

"Catching" so the caller, this mobile system can perform any function for managing a subscriber connection, in particular, to associate it with any necessary attackers room to install "weak" cryptoalgorithm encryption or to cancel the encryption for this session connection, and more.
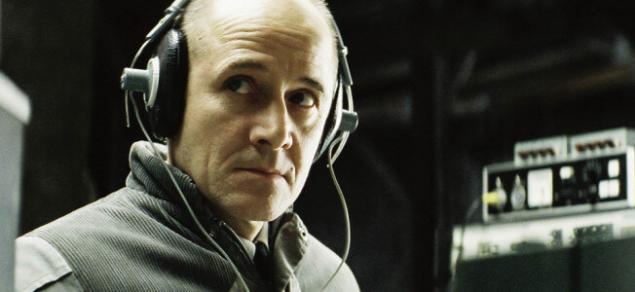
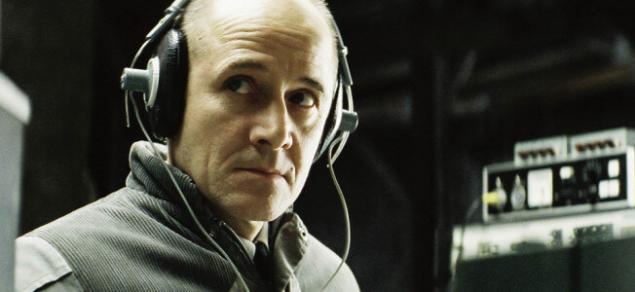
As an example of such listening can bring events early 2014 in the center of Kiev. During the mass protests against Yanukovych's regime, the crowd seized the car with employees of the SBU, which was conducted "the wire" frequency radios and phones of protesters. How does such equipment is clearly visible in the picture.
There is a third possibility for eavesdropping and interception of the mobile subscriber. On your smartphone victims need to install virus software. With the installation of the malicious software, attackers can "own" to select or clear all the encryption algorithm, unauthorized transfer (or destroy) confidential information of subscriber and many more.
How to determine that the phone is tappedAs told AIN.UA in "MTS Ukraine", directly to determine whether bugged at the moment, the phone is impossible, but an indirect evidence of a certain probability that you can. Many models of the old push-button phones even display a special icon (closed or open padlock), which demonstrated that currently used encryption of the conversation or not.
In modern phones, this feature is not provided. However, for smartphones there are special applications that can inform the user about the configuration settings of the current session, including whether it is passed it openly or with the use of the encryption algorithm. Here are some of them:
EAGLE Securityis a Powerful software to protect phones from eavesdropping. It allows to prevent the false connection to the base station by verifying the signature and the IDs of the base stations. In addition, it keeps track of the location of the stations, if any base station is moved around the city, or periodically disappears from its place, it is marked as suspicious, and the program notifies you. With this program, you can also get the complete list of apps that have access to microphone and camera of your phone and to prevent access to unwanted software.
DarshakProgram helps to monitor any suspicious activity of the cellular network, including the SMS that are sent without the user's knowledge. The program also evaluates the security of the network in real-time, shows which algorithms are used to encrypt the conversation and more.
Android IMSI-Catcher DetectorAnother software package that allows you to protect your smartphone from connecting to about base stations. However he has a small drawback — the app is missing from Google Play and installing it will have little trouble.
CatcherCatcherCatcherCatcherтак the same as the Android IMSI-Catcher Detector allows to distinguish the real base station from the false.
In addition, MTS is recommended to use the apps for security, including to encrypt conversations. For example, among anonymous web browsers can be noted Orbot or Orweb. There are also applications for encryption of telephone conversations, photographs and many secure messengers. published
P. S. And remember, only by changing their consumption — together we change the world! © Join us at Facebook , Vkontakte, Odnoklassniki
Source: ain.ua/2014/09/29/542567
Surprisingly, many market participants to respond to these questions was not a full answer we only got from "MTS Ukraine". Life :) has not responded to the request at all, and in Kyivstar, said that the operator is not an expert in such matters, therefore advised to address for comments to representatives of civil service. In addition to the responses of MTS, we used the information about surveillance from public sources.
As operators protect their networkTechnology GSM was originally developed and implemented taking into account the requirements of state authorities on the level of security. To maintain this security, most countries in the world prohibit the use and sell of powerful encoders, scramblers, cryptobranchoidea, as well as a very secure technology public relations. Themselves operators protect their radio channels by means of encryption, using quite complex algorithms. The choice of cryptoalgorithm is at the stage of establishing a connection between the subscriber and the base station. As for the probability of information leakage of user from equipment operators, MTS argued that it is reduced to zero because of the complexity and testability of object access and equipment.
How to "listen" phones

There are two methods of listening to customers — active and passive. For passive listening subscriber would require the use of expensive equipment and specially trained personnel. Now on the grey market you can buy complexes with the help of which you can listen to subscribers within a radius of 500 meters, the cost starts from several hundred thousand euros. They look like the picture on the right. The Internet easily can altipiani such systems and how they work.
Manufacturers of such equipment claim that the system allows you to monitor GSM calls in real time, based on access to the SIM card of the object or the database operator. If such access is not, the conversations you can listen to with a delay, depending on the level of encryption used by the operator.The system can also be part of the mobile complex to monitor and listen to the moving objects.
The second way of listening isactive essential intervention in the management protocols and authentication with the help of special mobile complexes. Such equipment, despite its apparent simplicity (in fact, this is a pair of modified phones and computer), can cost from a few tens to hundreds of thousands of dollars. Working with such systems requires highly skilled personnel in the field of communications.
The principle of this attack is the following: the mobile complex due to a closer location to the subscriber (up to 500 m) can "capture" signals for connection establishment and data transfer, replacing the nearest base station. In fact, the complex becomes a "mediator" between the subscriber and the base station with all its attendant security problems.

"Catching" so the caller, this mobile system can perform any function for managing a subscriber connection, in particular, to associate it with any necessary attackers room to install "weak" cryptoalgorithm encryption or to cancel the encryption for this session connection, and more.
As an example of such listening can bring events early 2014 in the center of Kiev. During the mass protests against Yanukovych's regime, the crowd seized the car with employees of the SBU, which was conducted "the wire" frequency radios and phones of protesters. How does such equipment is clearly visible in the picture.
There is a third possibility for eavesdropping and interception of the mobile subscriber. On your smartphone victims need to install virus software. With the installation of the malicious software, attackers can "own" to select or clear all the encryption algorithm, unauthorized transfer (or destroy) confidential information of subscriber and many more.
How to determine that the phone is tappedAs told AIN.UA in "MTS Ukraine", directly to determine whether bugged at the moment, the phone is impossible, but an indirect evidence of a certain probability that you can. Many models of the old push-button phones even display a special icon (closed or open padlock), which demonstrated that currently used encryption of the conversation or not.
In modern phones, this feature is not provided. However, for smartphones there are special applications that can inform the user about the configuration settings of the current session, including whether it is passed it openly or with the use of the encryption algorithm. Here are some of them:
EAGLE Securityis a Powerful software to protect phones from eavesdropping. It allows to prevent the false connection to the base station by verifying the signature and the IDs of the base stations. In addition, it keeps track of the location of the stations, if any base station is moved around the city, or periodically disappears from its place, it is marked as suspicious, and the program notifies you. With this program, you can also get the complete list of apps that have access to microphone and camera of your phone and to prevent access to unwanted software.
DarshakProgram helps to monitor any suspicious activity of the cellular network, including the SMS that are sent without the user's knowledge. The program also evaluates the security of the network in real-time, shows which algorithms are used to encrypt the conversation and more.
Android IMSI-Catcher DetectorAnother software package that allows you to protect your smartphone from connecting to about base stations. However he has a small drawback — the app is missing from Google Play and installing it will have little trouble.
CatcherCatcherCatcherCatcherтак the same as the Android IMSI-Catcher Detector allows to distinguish the real base station from the false.
In addition, MTS is recommended to use the apps for security, including to encrypt conversations. For example, among anonymous web browsers can be noted Orbot or Orweb. There are also applications for encryption of telephone conversations, photographs and many secure messengers. published
P. S. And remember, only by changing their consumption — together we change the world! © Join us at Facebook , Vkontakte, Odnoklassniki
Source: ain.ua/2014/09/29/542567
Carpaccio of Jerusalem artichoke
A spoon for mom... Or how we're teaching kids wrong eating behaviors.