896
Spyware officially uses the police in 30 countries
Surveillance of citizens from the government and the secret installation of malware on users phones - this is not science fiction, and not some conspiracy theory, but a common practice in everyday law enforcement activities.
Mikko Hyuppёnen (Mikko Hypponen), director of research at the Finnish antivirus company F-Secure выступил a report on hacker conference Black Hat, which is taking place these days in Las Vegas. In his speech he said that spyware officially used by police in at least 30 countries.
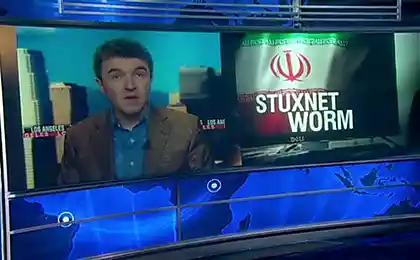
Actually, the history of malicious programs created for public use, conducted since the discovery of Stuxnet - probably the first of the virus made under the direct supervision of the President in the operation codenamed «Олимпийские Games ».
"More recently, the idea that democratic Western government will be involved in writing malware seemed ridiculous - says Hyuppёnen. - The idea that one democratic Western state will develop a spyware program to spy on another democracy? That is what we are seeing now ».
Mikko Hyuppёnen says that public services there are several reasons for the development of malware. This operatively-search activity, commercial intelligence, surveillance of citizens, sabotage and cyber war.
For example, in Finland the police now have the right to legally install spyware on your mobile phone citizen who is suspected of committing crimes. Seriousness of the offense and the degree of confidence in citizen involvement remain at the discretion of the police.
Mikko Hyuppёnen believes that this practice is unacceptable. Especially when it turns out that the surveillance was carried out for an innocent man. "I'd like to see [in this situation], they apologized. It will be fair, "- he said.
In addition to Stuxnet, the expert cited several examples of other malicious programs developed by order of the state bodies: among them Gauss, FinFisher, Flame and Careto.
To install malware on smartphones citizens used a variety of methods, including fake digital certificates with which redirected traffic from legitimate sites to sites with Exploit packs, Hyuppёnen said, citing the case of hacking CA Diginotar in 2011, when the attackers were able to generate codes digital certificates for many sites, including Google, Mozilla, Twitter and Microsoft.
Source: habrahabr.ru/post/232723/
Mikko Hyuppёnen (Mikko Hypponen), director of research at the Finnish antivirus company F-Secure выступил a report on hacker conference Black Hat, which is taking place these days in Las Vegas. In his speech he said that spyware officially used by police in at least 30 countries.
Actually, the history of malicious programs created for public use, conducted since the discovery of Stuxnet - probably the first of the virus made under the direct supervision of the President in the operation codenamed «Олимпийские Games ».
"More recently, the idea that democratic Western government will be involved in writing malware seemed ridiculous - says Hyuppёnen. - The idea that one democratic Western state will develop a spyware program to spy on another democracy? That is what we are seeing now ».
Mikko Hyuppёnen says that public services there are several reasons for the development of malware. This operatively-search activity, commercial intelligence, surveillance of citizens, sabotage and cyber war.
For example, in Finland the police now have the right to legally install spyware on your mobile phone citizen who is suspected of committing crimes. Seriousness of the offense and the degree of confidence in citizen involvement remain at the discretion of the police.
Mikko Hyuppёnen believes that this practice is unacceptable. Especially when it turns out that the surveillance was carried out for an innocent man. "I'd like to see [in this situation], they apologized. It will be fair, "- he said.
In addition to Stuxnet, the expert cited several examples of other malicious programs developed by order of the state bodies: among them Gauss, FinFisher, Flame and Careto.
To install malware on smartphones citizens used a variety of methods, including fake digital certificates with which redirected traffic from legitimate sites to sites with Exploit packs, Hyuppёnen said, citing the case of hacking CA Diginotar in 2011, when the attackers were able to generate codes digital certificates for many sites, including Google, Mozilla, Twitter and Microsoft.
Source: habrahabr.ru/post/232723/