554
How hackers protect their children from other hackers
Despite the promoted Hollywood movies, the stereotypes, most hackers — not one of those who with a maniacal laugh, conjure binary, emptying another jar of energy, and not one of those who checks the safety of every baby monitors or laptop in the country.
But experienced in the field of high technologies perverts, criminals and thieves accounts do exist, so that a portion of the parent technophobia is justified.

Chris Hadnagy – chief human hacker of Social-Engineer, and a father who wants to make sure that you are thinking about such things. He compares worry about the hacking attack against you, with concern about the possible emergence of a ninja on the front lawn of your house. Could it happen? Completely. Whether this will happen in reality? Not if your name's not Chuck Norris.
Instead Hadnagy advises to concentrate on more mundane things, which previously you could not think. "I'm worried about devices with known vulnerabilities, which are in my network."
Hacking the system geotagging
What it is: geotagging services are those services that add to the shot to your smartphone snapshots of the coordinates of the place where they are made. This puts your children at risk. Hadnagy says to turn on geotagging if, for example, you go on a vacation to Disneyland because you don't live there permanently. But what if you, say, place in the social network a photo of his child on the porch of the school? The stranger a dot appears on the map.
How to protect yourself: Hadnagy tries not to exaggerate the likelihood that this will happen with you, after all this, someone will have to find information in the caption to the photo in the social network. However, to data is becoming easier. To change the settings for geolocation for camera phone extremely easy, so do it.

Hacking Wi-Fi network
What it is: Even the guy who called his home network MakeAmericaGreatAgain, came up with a rather long password (It's 5ecretlyV0ting7orHillary) for protection. But most likely, he did nothing to protect the router that you can reset to factory settings by using the basic password.
How to protect yourself:
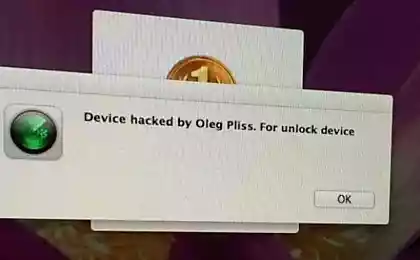
Hacking into password Manager
What it is: a strong password is a good deterrent just as the presence of a pit bull Terrier near the house will cause thieves to think several times before you get into your house. But passwords are too long, difficult to remember, and no one wants to waste time on it.
To organization password perfect program managers. Most importantly, you should not store the master file in the cloud, because the data from there to be kidnapped, and if that happens to you, you are waiting for really bad news.
How to defend: "[This file] should be on your hard drive in encrypted form, says Hadnagy. — Their customers I say, “no One wants to remember 50 passwords. Use a password Manager, and you will need to know a few shortcuts"".
Hacking Bluetooth
What it is: What is the worst thing can do Hadnagy if your phone has a Bluetooth connection? "I could turn on the microphone on your smartphone and listen to you. People think that it needs to be in the area of the antenna, but I can be a kilometer away from you," he says. Of course, Hadnagy agreed that such an attack requires preparation and target selection in advance. Hackers do not roam the streets looking for people with an open Bluetooth connection. They sit in Starbucks.
How to defend: "If the device you're connecting to] produces the standard code is 0000, it is vulnerable, he says. — If you specify a unique code, all right."
Hacking baby monitors
What it is: basically, to hack hackers use Cams in one of two ways: a) digging into Google or b) downloading the user's manual (the same document that you have just used to protect the router).

Hacking credit card
What it is: Adults may fear various forms of phishing, but there is another kind of identity theft aimed at people who have not yet took on the burden of education loans or mortgages. "I have two children and I have never seen any of their reports on loans, says Hadnagy. — However, if someone tampered with the personal data of my daughter, we learn [about the hacking], only when she turns 18 and she will receive the first credit card."
If you find out someone's name, date of birth and passport number, you can make fake documents. These documents can be submitted in a company that produces credit cards, because these data there is usually not checked. Six months your child has a perfect credit rating, and then — pam-pam some con man rides a boat on the Caspian sea at your expense.
See also: do I Need to tape up the webcam on laptops
Find out what is behind an obsessive craving for certain tastes and foods
How to protect yourself: If your data has been compromised, you can contact one of the credit companies to freeze your child's account for 90 days, which excludes any transactions on it. It's a quick fix, but you need to be prepared that you will have to spend a lot of time to negotiate with the credit organization, to once again restore the solvency of your child.published
Author: Alexey Zenkov
P. S. And remember, only by changing their consumption — together we change the world! ©
Source: rusbase.com/story/how-to-protect-your-family-against-hackers/
But experienced in the field of high technologies perverts, criminals and thieves accounts do exist, so that a portion of the parent technophobia is justified.

Chris Hadnagy – chief human hacker of Social-Engineer, and a father who wants to make sure that you are thinking about such things. He compares worry about the hacking attack against you, with concern about the possible emergence of a ninja on the front lawn of your house. Could it happen? Completely. Whether this will happen in reality? Not if your name's not Chuck Norris.
Instead Hadnagy advises to concentrate on more mundane things, which previously you could not think. "I'm worried about devices with known vulnerabilities, which are in my network."
Hacking the system geotagging
What it is: geotagging services are those services that add to the shot to your smartphone snapshots of the coordinates of the place where they are made. This puts your children at risk. Hadnagy says to turn on geotagging if, for example, you go on a vacation to Disneyland because you don't live there permanently. But what if you, say, place in the social network a photo of his child on the porch of the school? The stranger a dot appears on the map.
How to protect yourself: Hadnagy tries not to exaggerate the likelihood that this will happen with you, after all this, someone will have to find information in the caption to the photo in the social network. However, to data is becoming easier. To change the settings for geolocation for camera phone extremely easy, so do it.

Hacking Wi-Fi network
What it is: Even the guy who called his home network MakeAmericaGreatAgain, came up with a rather long password (It's 5ecretlyV0ting7orHillary) for protection. But most likely, he did nothing to protect the router that you can reset to factory settings by using the basic password.
How to protect yourself:
- First, make sure that you have installed the encryption method WPA2 (Wi-Fi Protection Access). If you have selected more primitive WEP (Wireless Encryption Protocol), you're more likely to live in 2002.
- There is a difference between the protected network to which you connect from the laptop, and the router that this network creates and which still set the password for remote access "password"). Open the user manual for your router and fix it.
- When you are on a network, disable the remote access feature. If you need to change the settings, use the cable.
Hacking into password Manager
What it is: a strong password is a good deterrent just as the presence of a pit bull Terrier near the house will cause thieves to think several times before you get into your house. But passwords are too long, difficult to remember, and no one wants to waste time on it.
To organization password perfect program managers. Most importantly, you should not store the master file in the cloud, because the data from there to be kidnapped, and if that happens to you, you are waiting for really bad news.
How to defend: "[This file] should be on your hard drive in encrypted form, says Hadnagy. — Their customers I say, “no One wants to remember 50 passwords. Use a password Manager, and you will need to know a few shortcuts"".
Hacking Bluetooth
What it is: What is the worst thing can do Hadnagy if your phone has a Bluetooth connection? "I could turn on the microphone on your smartphone and listen to you. People think that it needs to be in the area of the antenna, but I can be a kilometer away from you," he says. Of course, Hadnagy agreed that such an attack requires preparation and target selection in advance. Hackers do not roam the streets looking for people with an open Bluetooth connection. They sit in Starbucks.
How to defend: "If the device you're connecting to] produces the standard code is 0000, it is vulnerable, he says. — If you specify a unique code, all right."
Hacking baby monitors
What it is: basically, to hack hackers use Cams in one of two ways: a) digging into Google or b) downloading the user's manual (the same document that you have just used to protect the router).
- Digging. The essence of this method in a simple search for public cameras in Google. For example, if cameras from D-Link 'are always composed of words and Dlink number of the device, hackers can easily find accommodation and find the' open cells.
- The user's manual. One basic, but often overlooked way to get access. Every owner of a camera sooner or later forgets the password, so the data for recovery of password in the manual and these instructions are waiting for them, someone will use it. How to protect yourself: When you decide to spy on your child, make sure that you are the only one who does it. Hadnagy allocates 3 parameters which you can select the more secure the monitor:
- Select a camera with many settings. A simple change of the login and password immediately after purchase won't help if attackers have downloaded the user manual.
- May you have the ability to disable the device remotely. With any technology, the simple disconnection from the mains is always the most effective way to stop the rise of the machines.
- Address of the camera, inaccessible from the public Network. If you are so just observe your child using the computer, it is possible that the same can be done by other people.

Hacking credit card
What it is: Adults may fear various forms of phishing, but there is another kind of identity theft aimed at people who have not yet took on the burden of education loans or mortgages. "I have two children and I have never seen any of their reports on loans, says Hadnagy. — However, if someone tampered with the personal data of my daughter, we learn [about the hacking], only when she turns 18 and she will receive the first credit card."
If you find out someone's name, date of birth and passport number, you can make fake documents. These documents can be submitted in a company that produces credit cards, because these data there is usually not checked. Six months your child has a perfect credit rating, and then — pam-pam some con man rides a boat on the Caspian sea at your expense.
See also: do I Need to tape up the webcam on laptops
Find out what is behind an obsessive craving for certain tastes and foods
How to protect yourself: If your data has been compromised, you can contact one of the credit companies to freeze your child's account for 90 days, which excludes any transactions on it. It's a quick fix, but you need to be prepared that you will have to spend a lot of time to negotiate with the credit organization, to once again restore the solvency of your child.published
Author: Alexey Zenkov
P. S. And remember, only by changing their consumption — together we change the world! ©
Source: rusbase.com/story/how-to-protect-your-family-against-hackers/
Middle-aged women: how to become a "poor aunt"
The effect of plants on the chakras — balance the mind, body and spirit